Here is Apple's official 'jailbroken' iPhone for security researchers

Smashed iPhones are seen during COP28 in Dubai, United Arab Emirates on November 30, 2023. Image Credits: Beata Zawrzel/NurPhoto via Getty Images
In 2019, Apple announced it would start sending some security researchers a “special” version of the iPhone designed to be used to find vulnerabilities, which could then be reported to Apple so the company could fix them. In 2020, the company started shipping the devices, which are designed to have some security features disabled, making it easier for researchers to hunt bugs in iOS.
Before these devices existed, there was a loosely organized group of hackers and security researchers who were hell-bent on removing the restrictions Apple put on iPhones, known as the "jailbreakers." The term came from the concept of breaking out of Apple’s security restrictions — dubbed a "jail" — on the iPhone.
The jailbreaker’s goals were sometimes just to have fun getting around restrictions, such as sideloading apps not included in the official App Store, and — back in the day — to simply change the iPhone’s background before that feature was enabled.
Despite these seemingly innocuous goals, Apple waged war against the jailbreakers for years, discouraging people from disabling the security features of their iPhones. There is still at least one Apple support page that calls jailbreaking “unauthorized modifications” to iOS.
As for these days, Apple appears to have embraced the term jailbreaking by using it in the official instructions of the Security Research Device, according to a picture posted on X (previously Twitter) by security researcher Gergely Kalman.
“We've made it simple to get your existing tooling running on the Security Research Device. Through the cryptex subsystem, you can side load your tooling and it will run with platform privilege and any entitlement you'd like,” the instructions read. “This allows the rest of the security policies to remain enabled, providing the flexibility of a jailbroken device, while keeping the systems you're investigating intact in a customer-like state.”

An iPhone Security Research Device with stickers and instructions. Image Credits: Gergely Kalman
Kalman included a picture of the box holding his iPhone Security Research Device, a page of instructions for researchers and three stickers that he said were inside the box.
“Sorry no unboxing video, but here is the Apple Security Research Device with the swag that was included,” Kalman wrote in the post that he published on Tuesday.
It’s unclear how many of these Security Research Devices actually exist in the wild, and very few pictures of it have been widely distributed online.
Apple spokesperson Scott Radcliffe did not respond to a request for comment when TechCrunch asked how many of these devices Apple has sent out, and whether the program has led to an increase in the number of vulnerabilities reported to the company.
Kalman told TechCrunch that his Security Research Device is “identical” to an iPhone 14 Pro. The only difference, he added, is that at the bottom of the locked screen there is the writing “Security Research Device” and an Apple phone number, presumably to report it if it gets lost.
Apart from that, Kalman said there’s a special tag on the box that says “Do not remove” and “Property of Apple Inc.,” along with a serial number, which Apple notes on its website. Kalman said there is also a marking on the side of the phone which says: "Property of Apple. Confidential and Proprietary. Call +1 877 595 1125."
Before Kalman’s post on Tuesday, it appears that there was only one blog post that showed pictures of a Security Research Device, published in 2022.
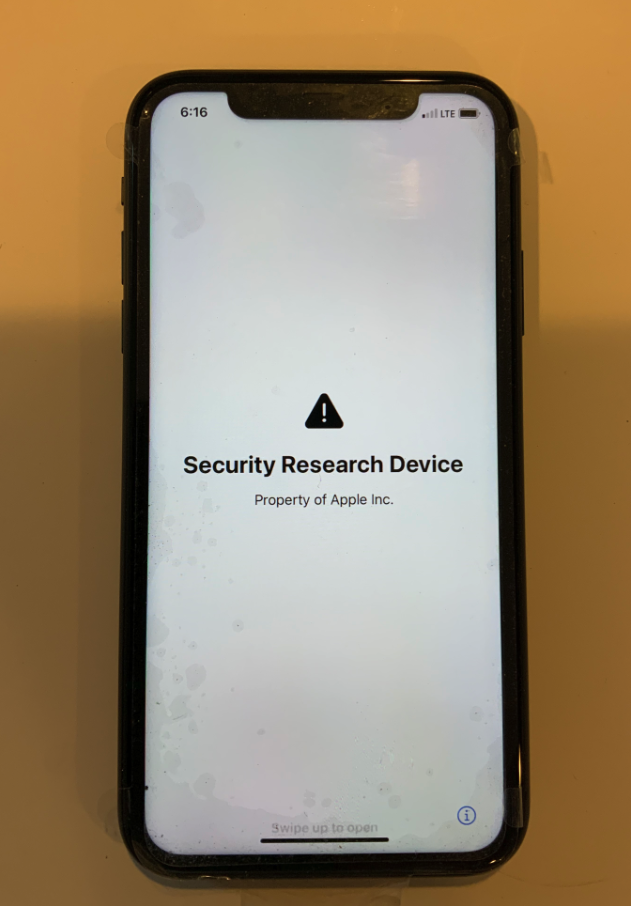
An iPhone Security Research Device. Image Credits: Hoyt LLC
The launch of the Security Research Device program was at least in part a response to the proliferation of iPhone prototypes — technically called “dev-fused” devices — that hackers and collectors were buying and selling in an underground market.
These "dev-fused" devices are essentially iPhones that have not gone through the complete production process, or were previously used internally at Apple to test features, and never intended to end up in the hands of consumers. As such, these devices have fewer of the typical security features and restrictions found on a regular iPhone. This is what made them particularly appealing for security researchers: these devices make it easier for hackers to find bugs in the iPhone’s most-guarded code.
That’s why these devices can cost thousands of dollars, and why Apple has been cracking down on this gray market — as well as offering the alternative Security Research Devices.
 Yahoo Movies
Yahoo Movies 
